Recent thoughts and media appearances
-
Notional architecture for modern IAM: Part 3 of 4
Welcome back to part 3 of my thoughts on enterprise patterns for modern IAM. Last week I provided a few techniques for thinking about the systems that you need to protect and optimizing controls for them. That included identifying which kind of policy (admin-, run-, or event-time) was most important for which kind of system as well as some thoughts on policy complexity per type of system to be protected.
This week I want to present what I believe is a conceptual architecture for modern IAM. It feels very different from the kinds of IAM infrastructure architectures you might be familiar with. It is, in some sense, a higher level architecture into which you would place classical components such as IGA or an IDP. But instead of me presenting it here, read on and discover!
Read more -
Optimizing controls to enterprise resources: Part 2 of 4
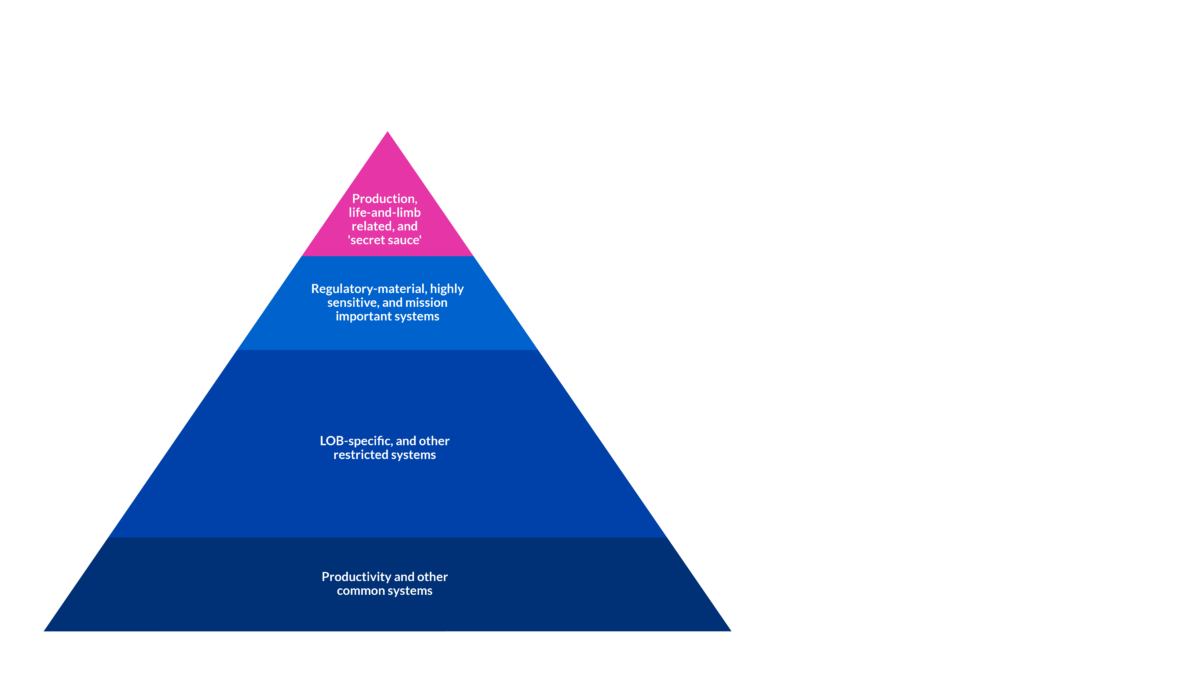
Last week I published part one of my four part series on “Enterprise Patterns for Modern IAM” in which I discussed the principles that should inform the design of a modern IAM architecture. This week, in part 2, I am offering up a way to think about the kinds of systems your IAM architecture is meant to protect and a means to align controls to that goal.
Optimizing controls to enterprise resources
Armed with these principles, and before we get to every architect’s favorite thing—a boxes and arrows diagram—let’s consider a conceptual framework for the kinds of IAM controls that are required and the systems that those controls protect.
Read more -
Enterprise Patterns for Modern IAM: Part 1 of 4
Over the last few months I have been working on ideas about modern IAM architecture, what it contains, and how to think about it. This is the first of four posts that expand on my previous thoughts. This post will examine the principles that should inform a modern IAM architecture. The second post will offer up a way to think about the systems a modern IAM architecture enables and protects along with the controls it provides. The third post will describe a notional architecture that embodies the principles discussed next and allows for the deployment of IAM controls. Lastly, I will talk about how to get started building a modern IAM architecture.
Read more -
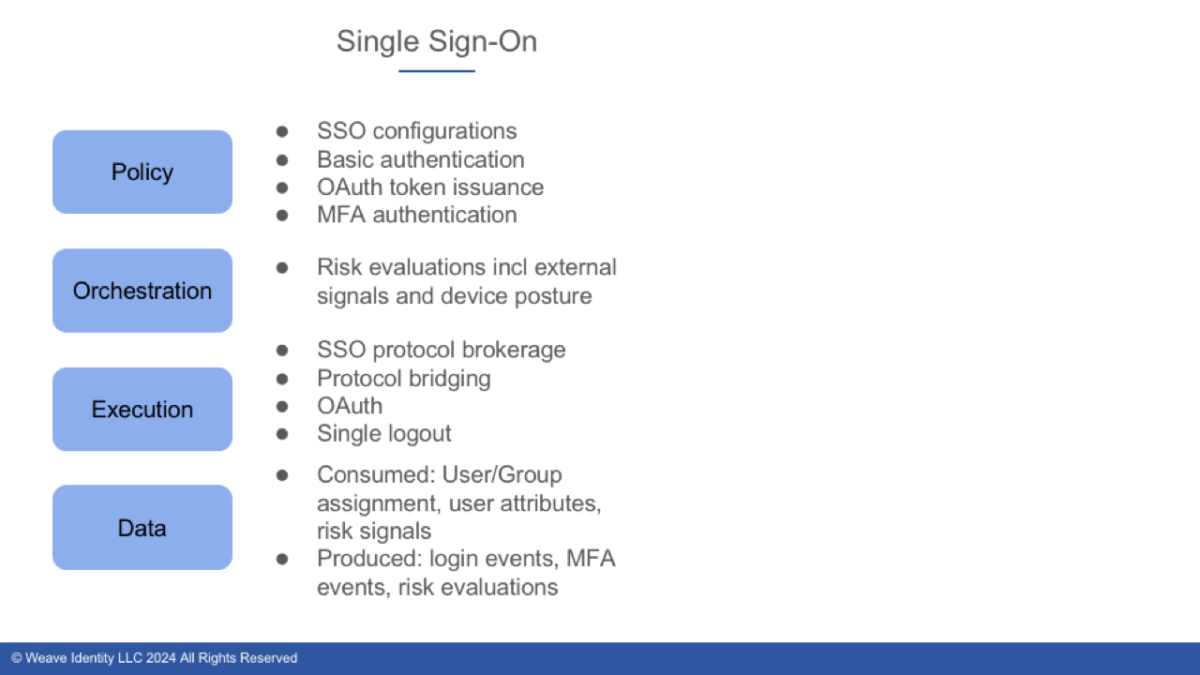
Putting the Four Components of Modern Identity to Work
Back in July, I fessed up to my struggle to understand current marketing definitions and boundaries in the IAM world. As part of my journey to clarity I proposed four components found in modern IAM architectures: policy, orchestration, execution, and data. I went on to then suggest, for good or evil, the notion of a workforce identity data platform which expanded on my ideas about the data tier of the modern IAM architecture. I now want to expand on the ways that you can use the four components of a modern IAM architecture to better understand your IAM world and approaches to augmenting and modernizing that world.
Read more -
The Rise and Future of Identity with Joseph Carson
I had an amazing opportunity to sit down with Joseph Carson. I have been a fan of his for a long, long time. We had a great time talking about everything from non-human identity to zero standing privilege, where AI comes into the mix, and much much more! Check it out!
https://player.captivate.fm/episode/6d6e49fb-9af5-4511-a586-1f7ad20a8f64